Cloud sprawl, otherwise known as Shadow Cloud or Bring Your Own Cloud, is an emerging problem for IT due to the growth of easy-to-set-up cloud providers. While typically a Shadow IT concern, it can also rear its ugly head thanks to a lack of IT policy and oversight into cloud usage.
What exactly is cloud sprawl? It’s unknown, unauthorized and unregulated cloud usage by the members of an organization.
You might think that for every 1 authorized cloud provider, you’d have 1-2 unauthorized cloud providers, meaning roughly 50% of your cloud usage is unauthorized.
Brace yourselves, because in all actuality, more than 80% percent of your current cloud providers are probably unauthorized per Cisco. For some companies, it can be 25 times what they estimated according to recent surveys.
All this said, it’s important to tackle this problem ASAP, before it becomes an unwieldy nightmare tomorrow.
How Not to Deal with Cloud Sprawl
Dropping the hammer and trying to directly shut off unauthorized cloud usage or even threatening it could crush your business — if you haven’t done your research first. For one, people could become jaded towards IT for trying to interfere with their job. On the other hand, it might throttle productivity as users try to comply with IT’s mandates, making once annoying obstacles back-breaking issues.
Ultimately, users will be forced to turn to IT, putting undue pressure on the department to maintain and ultimately lift productivity by finding new tools on a short deadline. It’s better to assess the situation first, as we discuss next.
How to Properly Deal With Cloud Sprawl
Another thing to keep a close eye out for is usage terms and user agreements. Some providers put in their user agreement that they own any data uploaded, so when you find these, make sure you do tell those users to cease usage immediately.
Now that you know which services you can keep using, it’s time to consolidate them across departments. Provide some case studies as to why individual departments have used those solutions, and why certain solutions are being shut off. Be careful not to place blame, even if it’s deserved, because that, again, will cause frustration with IT.
Consolidating to a limited product or range of cloud products will allow you some room to negotiate or at least receive a better value price with cloud service providers. Having 5,000 users on one product gives you more leverage than just 5. At the same time, there are typically price breaks as you scale up with these solutions.
Dealing with the Stragglers
Unfortunately, you’ll always have some stragglers, or folks who refuse to accept your policy, even after you’ve mandated certain solutions. While HR should have some disciplinary policies in any documents that the employee signed related to guidelines for workplace technology. The only way to truly shut down these individuals is through active monitoring of cloud sprawl.
According to J. Colin Petersen, President & CEO of J – I.T. Outsource, “the ONLY way to (almost) guarantee that your employees aren’t using the cloud is to block access by using web filtering and content blocking software to prevent them from using cloud domains such as Dropbox or OneDrive.”
What are some services you can use? Cisco has announced its Cloud Consumption Services, which has a free 30-day-trial and a price-per-user plan that should help you get a better idea of “what cloud services you’re using and protect your organization by reducing cloud risks and costs.”
These tools should help you identify connection methods and help you lock them down for good.
Moving to a Secure File Management Platform
Don’t want to deal with stragglers? You should have no patience for those using services that “own” your data after it’s uploaded, but for others putting up a justifiable fight, you might find that no other tools will work for them or you in IT. This might be because of functionality or because of the lack of insight into file activity and usage.
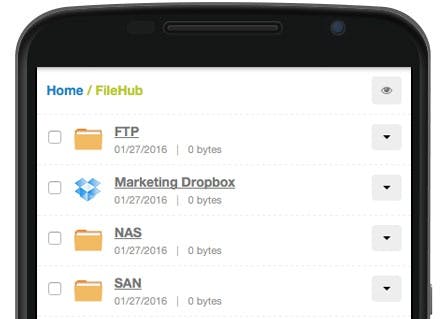
That’s when you need a File Management Platform like SmartFile — pardon my shameless plug — that can connect, audit, visualize and automate file lifecycles. Enterprise customers can link hosted storage and cloud services to SmartFile for advanced file management, regardless of where the files are hosted and how the users access them. This way, your users don’t change their behavior and you’ll gain a full audit trail on file activity and enhanced file functionality. Feel free to chat with sales if you’re interested in learning more.
Concluding Thoughts on Cloud Sprawl
Cloud Sprawl is a problem that’s not going to go away. Make sure you deal with crowd sprawl properly by interviewing key stakeholders and gaining insight into cloud usage before moving forward. Then you can choose whether you should deal with the headaches that come with your non-compliant employees or finally move to a secure file management platform that makes everyone in your organization happy.
