In June of 2010, a security company discovered a virus that was able to insert itself into the Programmable Logic Controller (PLC) of a Siemens Supervisory Control and Data Acquisition (SCADA) system. It was able to do all sorts of fun things since it penetrated so deeply that it could actually rewrite the command and control of the PLC itself.
Once identified, Siemens publicly announced that none of the customer’s SCADA systems had been affected. Of course, Siemens was referring to customers that had purchased these incredibly expensive computer systems legally.
Enter Iran. They were not legally allowed to possess Siemen’s SCADA systems due to the US embargo on technology, however, here they were secretly building a uranium enrichment program with the help of illegally purchased Siemens equipment.
You can imagine which specific SCADA systems worldwide were hit hardest with this infection. This virus, ultimately known as Stuxnet, single-handedly ground Iran’s nuclear program to a halt. Kaspersky Lab said it was so well done and so pervasive that there was no possible way it could have been created by anyone less than a major nation.
While neither the United States nor Israel took credit, it was later revealed that Stuxnet was a coordinated effort between the two nations. Both had a vested interest in stopping Iran from creating nuclear weapons.
They devised a way to shut down the program while making it look like Iran’s SCADA systems had issues or gremlins that prevented the illegally obtained equipment from doing what they wanted. This was a major score for both intelligence agencies and also acted as a proof concept for penetration and disruption of infrastructure. A few lines of code was all it took to physically bring down a nuclear reactor project.
The “Guardians of Peace” Hack Sony
Fast forward to November of 2014. A hacker group calling themselves the “Guardians of Peace” break into Sony Pictures and steal several films still in production, including “Still Alice” and “Annie”, as well as personal information and a large swath of emails that included many embarrassing disclosures Sony was forced to face.
Sony calls the FBI, who begins investigating the breach and starts working with security outfit FireEye to try and determine the origin of the attack and protect their network. In December of the same year, the FBI and FireEye confirm that the source of the attack is North Korea, and the “Guardians of Peace” hacker team is sponsored by the state. At this point, the damage is done. The hackers threaten more harm to Sony if they release their upcoming title “The Interview”, which is about two Americans going to interview North Korean leader Kim Jong Un. Sony bends to the demand and announces that “The Interview” will no longer be released on December 25th, 2015.
Ukraine’s Power Grid Goes Dark
In December of 2015, hackers hijacked 2 power distribution companies in Ukraine and were able to knock out power to more than 80,000 people. The hackers even went so far as to sabotage the computer systems that controlled the electrical grid so the restoration would require more manual intervention. Then, to throw fuel on the fire, they performed a telephone denial-of-service attack on the power company’s call center so few people could actually get through to report the outage.
This attack was diligently planned and very well executed using a known trojan infection that has been used in infrastructure attacks before. The Ukraine government blamed the Russian government, and while it would make sense, security firms deeply rooted in the investigation have yet to confirm this.
International Cyber Warfare
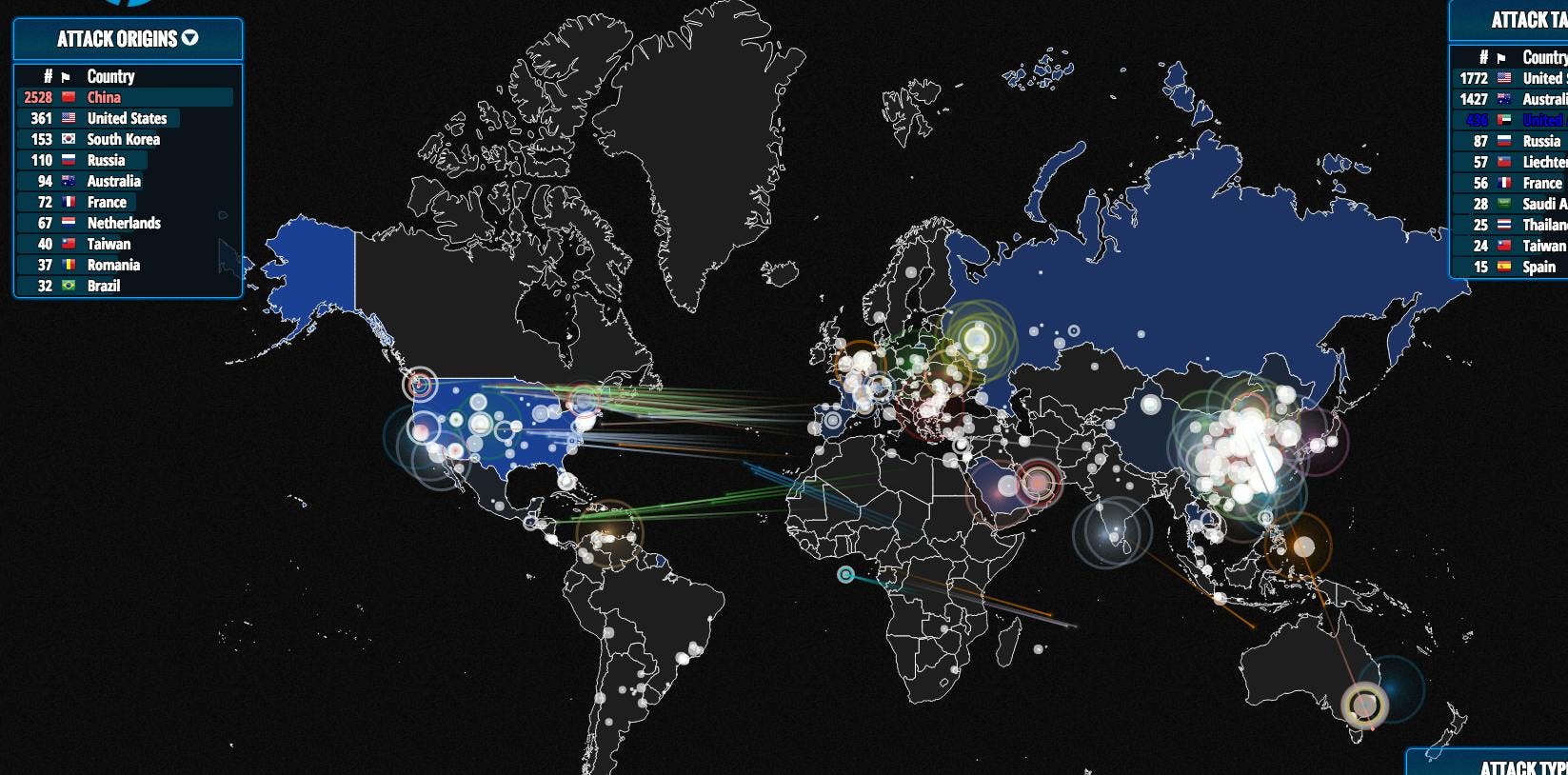
Every day there is a constant war going on pitting government against government, hackers against governments, governments against hackers, hackers against corporations, security firms against hackers and on and on.
Anyone can watch the larger attacks happen in real time. Simply go to http://hp.ipviking.com/ and watch the United States get attacked by everyone, and the United States attack right back. It’s a visual representation of the sheer flood of bandwidth that everyone is throwing at each other in an attempt to break down defenses, enter computer networks and steal or destroy data.
And this doesn’t even include the plethora of infections and malware being developed and sold in the cyber-arms bizarre that is the Dark Web. At any given time I can go window shopping for the latest and greatest attack methods and malicious code that I can custom tailor for my attack packages. Everything is for sale, and the largest arms dealer by far is the Russian mafia.
America’s Glaring Vulnerability
So how does all of this relate to why America’s infrastructure is seriously at risk, you ask? Quite simply, the above examples are the evidence as to why the USA and other major entities around the world are vulnerable. Iran was running a secret nuclear development program tightly under guard and it was destroyed. Sony, an owner of literally billions of dollars of intellectual property, was compromised by a hacker team sponsored by a state that is known for a collapsed economy, starvation and operating concentration camps. Ukraine’s power grid wasn’t secure enough to withstand an intrusion attack to the point where the hackers had infiltrated so deeply they could shut down the phone system.
The USA’s own infrastructure is in no better shape. We have a vast computing infrastructure that controls virtually every facet of our grid. Dams, traffic lights, phone systems, power and nuclear control to name a few. Heck, even the dog catcher is logged into a database somewhere. Maintaining this infrastructure is critical, not just to the continuing smooth operation of the United States and its commerce but also to its citizens.
We know we have a sagging physical infrastructure and haven’t maintained a proper budget to ensure that things like bridge collapse can never happen. Even John Oliver did a segment on this a while back. What this means is that we do not have a budget to maintain the computerized infrastructure that controls the crumbling physical infrastructure.
The Vast Majority of Our Computer Systems Are Hackable
Consider for a moment this hypothetical. Assume that the United States has 100,000 computer systems controlling every aspect of our infrastructure (we know this number is incredibly small compared to everything that is deployed at the local, state and federal level but let’s work with this easy number). Let’s also assume that the local, state and federal governments do not have the budgets to keep and maintain proper security on these computer systems; that they’re doing what many financially struggling companies do, which is to say “if it isn’t broken we aren’t touching it.”
What we have just created are 100,000 computers that can be compromised, infected and controlled. Now multiply that number by 10 or maybe even 50 or 100 and we have the whole of the US infrastructure we must maintain and secure to consider ourselves safe.A dedicated hacker, or hacker team, on a mission to destabilize the United States is not going to simply pick a target like a power station and bring it down. They’re going to try to get into as many systems as they can before they fear detection and then attack them all at once.
Or they’re going to be continuously trying to break into various systems surreptitiously while publicly attacking another so the limited resources of the government are diverted to attend to the public threat. Hacking takes time and the Hollywood version of “I’m hacking into the Matrix in sixty seconds” is totally bunk.
Hacking is a game of patience. Sometimes it will take me months to ethically hack into a client’s network for testing purposes. I will simply let my attack machines go and go until they report back that they’ve broken in. If a system is not kept up, like in the case of US infrastructure, then the job becomes easier because known vulnerabilities, and how to break them, are published publicly in multiple sites across the internet.
CyberAttacks: It’s Not If, But When
We are years behind in this endeavor and the hackers are using the latest and greatest in malware technology and techniques to penetrate our systems and, to top it off, there are various ways they can do it. They can inject payloads into file attachments in emails that have poor spam filtering. Compromise websites that are behind in patching so people that visit the sites have their computers injected with code. Pose as an IT company and get unsuspecting people to give them critical information because they didn’t receive proper training. They can even create a social media hack to cozy up to targets to understand who they are and then transfer them something malicious via files or links. The head of the CIA was compromised in a similar manner as well!
At this point it’s not “if” this kind of attack will happen, it’s “when” and unless the United States starts taking this issue seriously we, who live here, are at serious risk.
LOCK DOWN YOUR NETWORK
FREE PENETRATION TESTING COURSE
- Social engineering
- Port scanning
- SQL injecting
- Anti-virus evading
- Client side attacking