SmartFile has added new visualization and trending tools for our Enterprise customers. This feature release helps account administrators visualize and monitor audit trails, such as successful and failed login attempts, trending network file activity and all other SmartFile audit data points.
This new tool gives administrators new ways to monitor and ensure compliance. They can view past and real time audit data, enabling them to quickly identify unusual behaviors and outlying events.
The view can be filtered down to look at the user’s IP address or specific usernames to see the actions that were performed. Administrators can use this to see exactly when breach activities are occurring and what accounts are targeted.
With the new visualization and trending tool, reports and data can also be exported for additional business analysis through 3rd party tools.
Here’s a closer look at the new visualization tool:
Dashboard
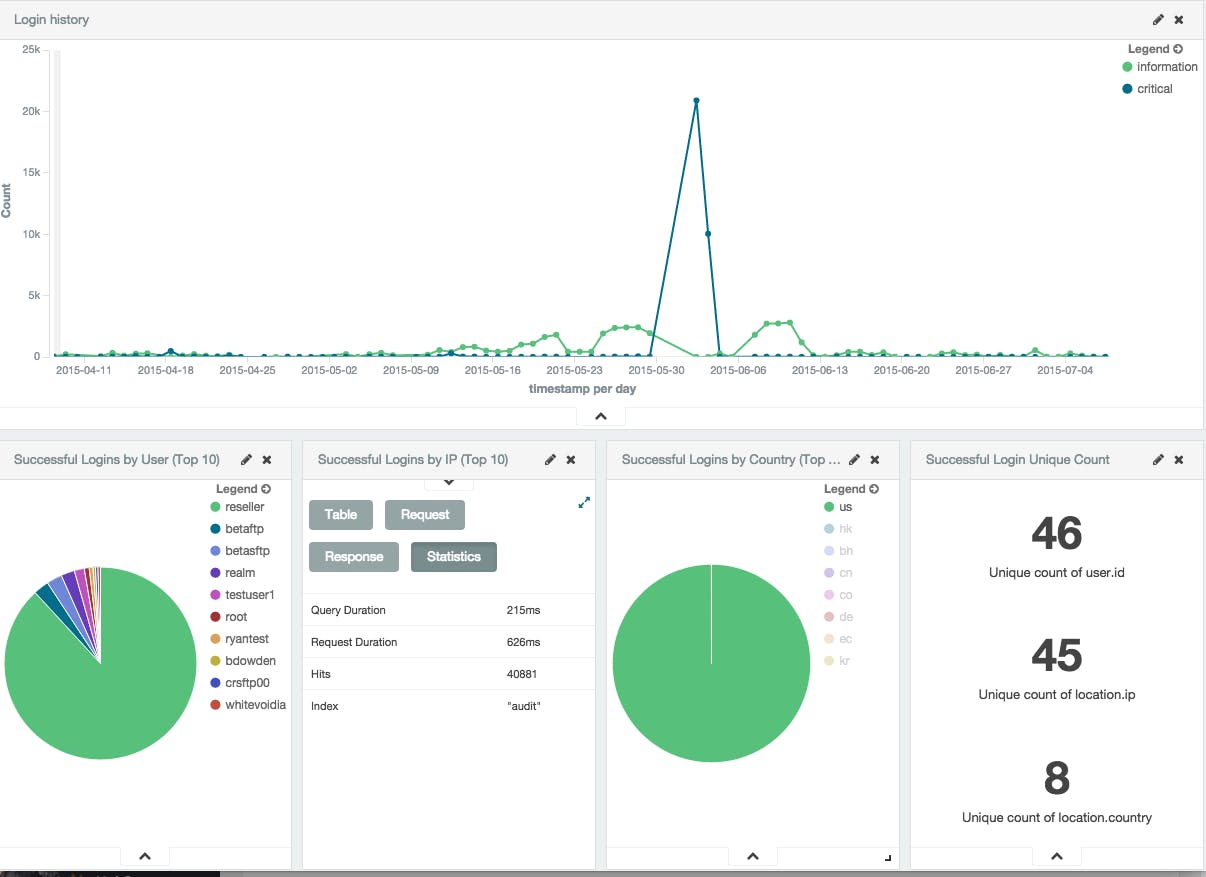
The dashboard gives you a large amount of data to look at without straining your eyes. You can view data in real time to identify spikes that are worth taking a closer look.
You can also take a look at your top users by login success or failure. It’s recommended to add failed logins to your tool so you can identify spikes and see which users are (a) having trouble or (b) being hacked.
Multiple Charts
We offer you a wide variety of charts to help you view and understand your audit data. Sometimes it’s worthwhile to look at data in a few different ways, whether that’s a pie chart, a table or graph.
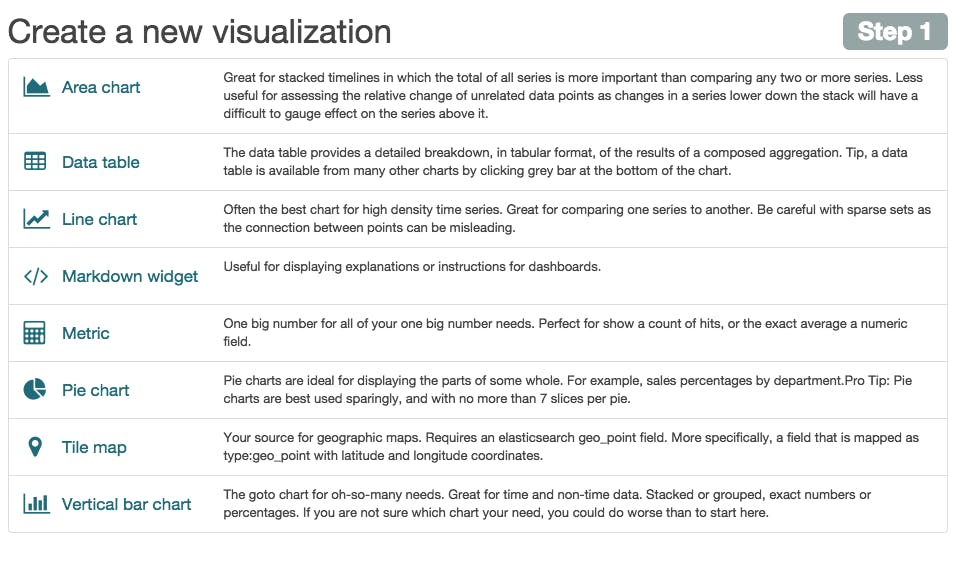
All in all, looking at data from different views will help you understand it better, so we’ve tried to give you several views.
Our VP of Products, Christopher Sheaves, elaborated on the release by saying, “SmartFile is focused on our customer’s needs, and the new visualization and trending features will help our on-premise customers view, manipulate and handle audit data. With this release, SmartFile continues to stay ahead of the competition in the business file sharing and management industry by giving I.T. new tools to monitor and identify compliance and security concerns…”
