There is a lot of misinformation out there about how to protect ourselves online and with cybersecurity. Many of us have heard and spread common misconceptions about what is and is not safe online. It’s an issue worth addressing since many of these myths need to be busted.
I’ve touched on, or dove deep, into some of these in my previous articles and our goal here today is to shed some light on some rather serious issues in our thinking when it comes to keeping safe in our technological bubbles. So, let’s begin, shall we?
Myth 1: Using free WiFi is safe if I’m on a known WiFi, right?
I get this question all the time. People love free WiFi and why shouldn’t they? They don’t have to use their mobile data plan, which saves them money, and it’s pretty much everywhere you go these days, coffee shops, restaurants, shopping malls, Mt. Everest, everywhere.
Users have a false sense of security when connecting to hotspots they know and trust. They see them regularly so they think they’re safe. Their devices may connect automatically and they know how to tell the difference between “Starbucks WiFi” and “Free Public WiFi” when it comes up on their connection list. So, what is there to worry about?
What most people do not realize is that a hacker doesn’t have to broadcast a fake wireless ID and hope some people will connect to it. We can set up the exact same WiFi name and make ourselves “Starbucks WiFi,” piggybacking off their connection and even the savvy user would never know the difference.
Do you normally get an “Accept Connection” welcome screen with the day’s date on it from your trusted free WiFi? I can do that, too! It’s called an “Evil Twin” attack and, in a nutshell, I connect my laptop to the hotspot I want to spoof and rebroadcast their signal.
When you connect to me, your device is now within a network I control and all of the data you pass back and forth to the various websites you visit are now captured by me. I can decrypt secured SSL connections and even probe your device to see if I can inject infections on it to steal your data later. Basically, if you’re connecting to my network, it’s so very easy to own your device.
Many places are aware that rogue WiFi signals can be broadcast to their patrons so they put up signs that say something like “Our WiFi name is ‘Starbucks WiFi’ and all other WiFi names cannot be trusted!” These signs are everywhere, even at The Forbidden City in China, which has a serious problem with hackers.
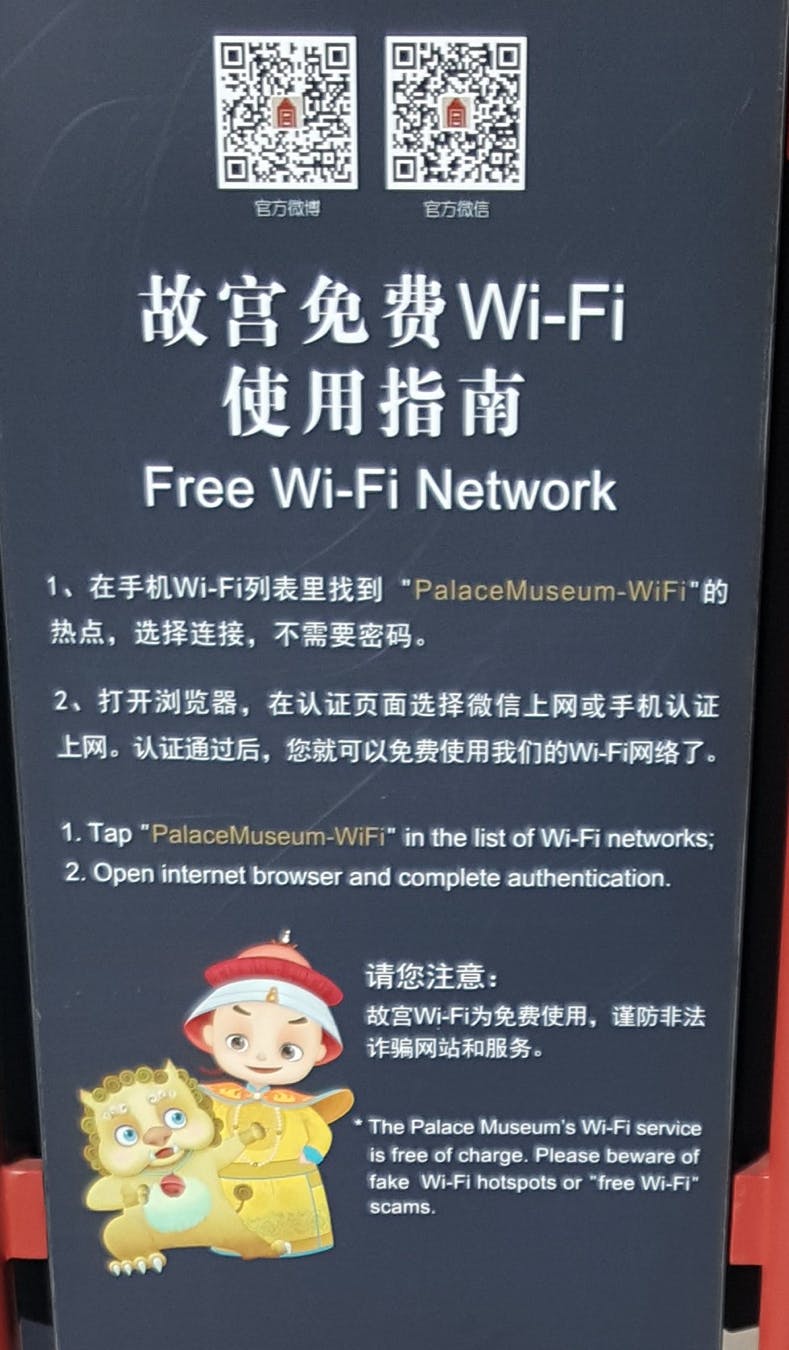
These places, though, give their patrons a false sense of security. The patron will see the legitimate WiFi name and connect to it. These signs are a hacker’s best friend as the institution offering the free WiFi has established the trust for them.
In an ideal world, we wouldn’t have to worry about things like this but this problem is rampant worldwide. With a little knowledge and free utilities anyone can download, this malicious spoof can be performed.
Myth 2: I have a virus scanner so I’m 100% protected against infections.
I’ve written rather extensively about this one before. In an article called “I Love Ransomware,” I take a deep dive into not only how ransomware infects a computer, but also how it so very easily bypasses virus scanners.
Consider for a moment that the developers of various ransomware infections are changing the code multiple times a day. Just read this recent monthly report on ransomware news and you’ll have an incredibly hard time keeping it straight!
Makers of traditional virus scanners are being outclassed daily, as the time it takes them to discover a new ransomware variant, create an inoculation and then get it to the users is slower than the incoming changes to said malicious code. It’s a reactive fight in a losing battle and they’re starting to recognize it.
So now we have next generation antivirus solutions on the market proactively trying to fill this gap. Cutting through the buzzwords like “Machine Learning” and “Artificial Intelligence,” these pieces of software take a whole new approach to threat detection.
Some inoculate in real time in the cloud, others don’t inoculate at all and instead look at unique characteristics of behavior within the computer’s operating system to try and stop infections before they can execute. Some appear to be fairly effective and others not so much.
We also can’t forget that the ransomware and malware developers don’t stop innovating and that their relationship with antivirus outfits, next generation or otherwise, is one big cat-and-mouse game that never stops.
It’s not “if” but “when” the next generation antivirus developers will once again have to switch up their methods, though the hope is that they’ve found a method for detection that is incredibly hard to defeat.
Myth 3: My computer is password-protected so I’m secure.
Surprisingly, at least to me, I still get this question quite a bit. Yes, a strong password is very important and will prevent the casual person from getting into your computer or device, but this method alone still leaves the computer incredibly insecure.
Basically, I can crack your Windows password in a matter of minutes. There are utilities out there designed to do this very thing and some even come with tech support if I can’t figure it out! I’ve had clients go wide-eyed in the past when we walk in, crack their password after they forget it, and then walk right back out.
Having your computer password-protected will not prevent data theft from a lost or stolen laptop or device. If your business falls under any kind of compliance, then odds are there is a good password in place but it’s just the tip of the iceberg. If your company stops there, you’re potentially in serious trouble.
Beyond simple passwords is encryption. Encryption is data’s best friend. By fully encrypting the complete hard drive of a computer with a good level of encryption (not all encryption is built the same), you are essentially protecting your data from being stolen if you ever lose your computer.
You can also go one step further and encrypt individual files that are sensitive, such as that password list you keep in Excel. Most applications that generate some kind of document, like Microsoft Office, offer built-in strong encryption for you to use.
Myth 4: But I use a Mac and those never get infected!
I bang my head against a wall every time I hear this one. This myth is so prevalent among Mac users that I chose to give it its own section in this article and not cram it into my earlier antivirus myth.
For decades, there has been this terrible false perception that Macs cannot be infected when, in fact, one of the first types of infections ever developed actually hit Macs BEFORE the IBM PC was ever created! I have to hand it to Steve Jobs and his marketing brilliance for this one.
While it’s true that for years Microsoft Windows has been the largest target for malicious code by far, Macs have had their fair share of viruses, Trojans and ransomware. In fact, Mac infections are steadily rising as Apple continues to sell Macbooks like they’re going out of style.
As imperfect as antivirus software is, it’s still a needed piece of software for what it can catch and this is true of Macs as well. If you’re not running any kind of protection on your Apple computer it is very possible you’re infected right now and simply don’t know it.
Every major antivirus maker has a Mac offering so please, for all that is holy, go get a virus scanner for your Mac! While antivirus is not wholly effective, see above, it still offers defense and no computer should be undefended in this day and age.
Myth 5: Mobile phones don’t get infected.
This one is a big problem and it’s only getting worse. If you read this article from 2013, you can see just how sharply infections on mobile devices rose in a single year. By the beginning of 2016, malware infections had exploded to an all-time high and that number has continued going up with this year having a 96% increase in infection rate over the previous year alone!
This is simply not an Android problem either. Another myth of mobile device infections is that Android, Google’s free open source operating system used by every manufacturer except for Apple, is the only one that gets infected since there is little control over the operating system or the Google Play Store.
Once again, Apple’s marketing machine is brilliant with this. Apple devices get infected too, and their rate of infection is increasing. Apple, to drive home the point that they believe their devices are way more secure, decided to remove all antivirus apps from their App Store. Their premise is the App Store is so secured and stringent that no malicious apps could be published there, therefore an Apple device cannot be infected.
This does their users a grave disservice because there have been known infected apps that were caught by Apple well after users were infected and apparently, no one in the decision-making process at Apple realized that a user can go to a website and download an infection accidentally.
It is true that Apple left the web filtering apps alone and just killed antivirus, but web filters are not 100% effective; if something does get past them there is no antiviral recourse Apple users have. In two words: it sucks.
Users need to be aware of what they download and where they go online but should have options for defending themselves on any platform they choose to use. If that platform limits their defensive capabilities, then the user should question if that platform is a wise choice for them.
A little knowledge can go a rather long way here. Let’s all do our best to make sure we stay alert and up to date.
