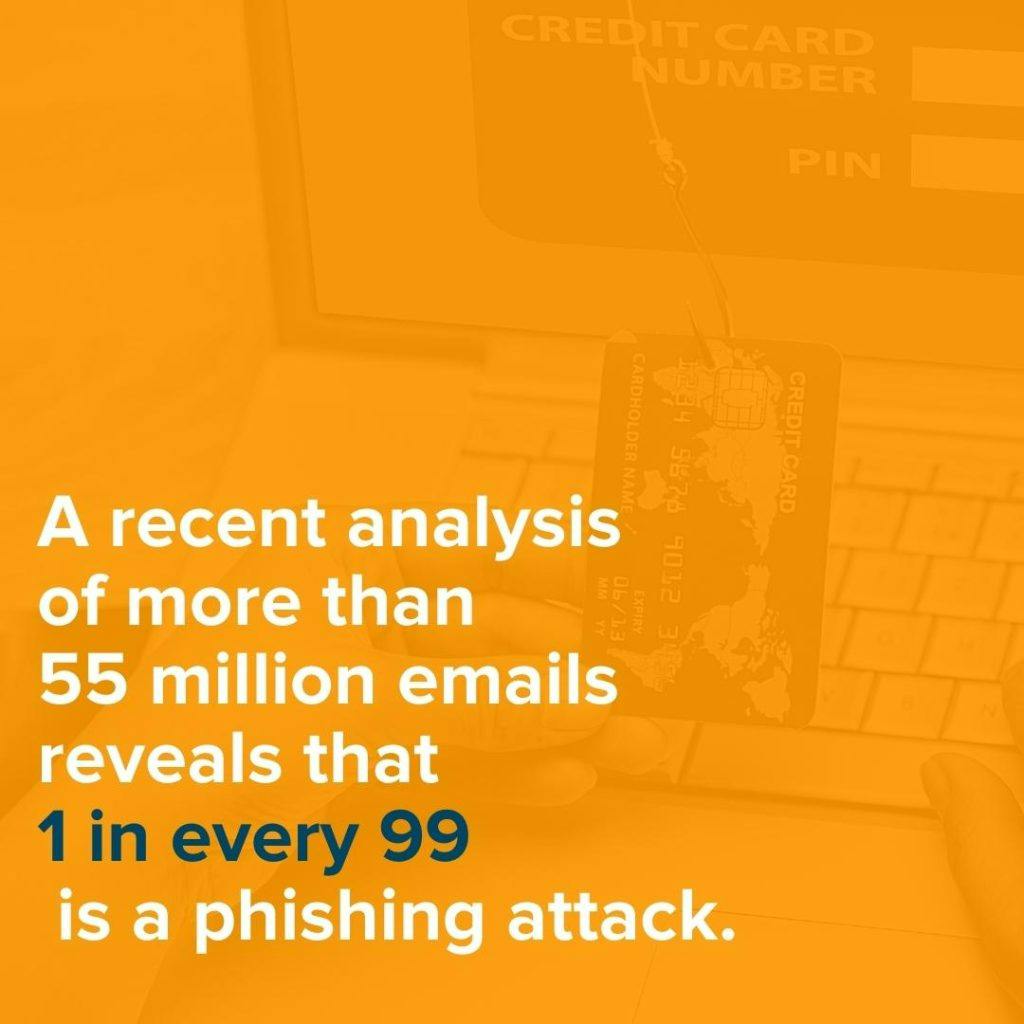
Are you worried about phishing or other social engineering attacks in your organization? In today’s cyberscape, you should be. Especially since a recent analysis of more than 55 million emails reveals that 1 in every 99 is a phishing attack.
While no one wants to fall victim to a phishing scam, the truth is, not enough people are properly educated on the matter. How can we protect ourselves from the ever-expanding threats that phishing presents without understanding the signs? Well, the answer is: we can’t.
No matter how great your cybersecurity precautions are, you’re only as secure as your “weakest link.” Unfortunately, these “weak links” within your organization are often well-intended employees who simply aren’t educated on what to look out for when it comes to phishing scams.
Considering it only takes one user to cost your company millions in lost data, lawsuits, and stolen intellectual property, it’s worthwhile to try to get your phishing click rate to as close to zero as possible. This is why training your employees on phishing emails and ransomware is so important.
To learn more about how you can set your organization up with the right know-how to decrease their phishing click rate, check out our six tips every organization should follow below.
1. Understand the Basics of Phishing
First and foremost, let’s break down what phishing is and how it came to be. The term “phishing” actually got its name when cybercriminals in the 1990s started sending out email “hooks” that were designed to get victims to “bite” and be “lured” along by ill-intended hackers.
Phishing is a type of social engineering attack that tricks a person or entity into sharing their sensitive information. It can also be a way to deploy malicious software on the victim’s computer, like ransomware.
Even though phishing scammers tend to target individuals, this can also have a major effect on your company if one of your employees is successfully targeted. If a phishing scam is posing as your company and convinces your employee to give up their personal credentials, a hacker could easily use that information to log onto your server posing as your employee to steal confidential information from your company. The best way to deal with this attack is to prevent it from happening in the first place. That’s why phishing awareness is so critical for today’s businesses of all shapes and sizes!
If you aren’t implementing some sort of cybersecurity training at your organization that educates about the adverse effects of phishing and why it should be taken seriously—put it on your to-do list!
2. Make Phishing Education Part of Your New Hire Training
By educating new employees on the importance of avoiding phishing scams, you show the importance of this subject right from the get-go. It’s important to remember that as soon as your new hire receives their computer equipment and starts working, they become an even greater target for a potential cyber attack.
The thing is, cybercriminals are scoping out victims every day—and any hacker knows what an easy target a new employee can be. These “bad actors” are even known to monitor companies’ LinkedIn profiles to spot and go after new hires.
The best way to ensure none of your employees fall victim to a phishing scam is to make cybersecurity training a priority from start to “finish.” Since these types of threats are ever-adapting, there is no “end” to phishing training. This training should continue and build upon itself over the course of employment at your company.
3. Train Employees to Examine Email Domains & Links Carefully
Here’s what your phishing education and ongoing training should cover to decrease your employee’s click rate:
Double (and Triple) Check Domains
If you’re getting what looks like a professional email from someone, but it is coming from a public domain, it could very well be a phishing email. In MOST cases, you won’t be receiving emails from a company like iTunes or Amazon with an address that ends in “Yahoo.com” or “Gmail.com.” Even Google won’t use Gmail! Any legitimate organization will have a professional domain attached to the end of the email account.
If the domain name matches the apparent sender of the email, the email is probably legitimate—but make sure you look carefully! Another sign to look out for when it comes to phishing attacks is a misspelled domain name. Since many cybercriminals know people are less likely to trust an email coming from a public domain, they may try to use a domain name that appears more legitimate.
Since the domain they’d like to use is owned by the company they’re trying to impersonate and can’t be used, they’ll purchase something close enough, hoping you won’t notice. For example, instead of receiving an email from “Amazon,” the domain name might use “Arnazon” instead. Did you catch the difference? It looks pretty similar! Hackers are banking on this oversight.
Think Before You Click
Make sure your employees understand that no one in your company will ever ask them to click a link or attachment without some additional context or direction. If you get an email from what appears to be someone in your company asking you to click a link or complete a download with little to no information accompanying the request—reach out to your supervisor for more information. In many cases, you’ll find that this request was sent from a bad actor that was just trying to lure you in.
Furthermore, there are many cases where cybercriminals will use deceptive links to direct someone to what they think is a valid web page but has actually been designed to steal their keystrokes. It’s important to remember that just because the text on the link says “Target.com,” the link itself may not match the website they THINK they are headed to.
Instead of clicking right away when you see link text in an email, teach your employees to hover over the link with your cursor before clicking. When this is done correctly, a box should appear where you can check and make sure the link actually matches up with the “Target.com” URL. If the URL looks phishy, think before you click and let your manager know!
4. Run Phishing Penetration Tests
You should consider running some white hat phishing tests internally to gauge how your team would be impacted by a phishing attack. Measuring the phishing click rate, otherwise known as the response rate, through a penetration test is important to understanding how dangerous phishing is to your business.
As users fall for your trap, alert them, and explain to them what they should have spotted. You can take a screenshot of the email and make notes or circle the aspects that should have indicated that this was a phishing attempt. This will be a good reference for your employees to have for the future.
In our article on social engineering attacks, Drew Parrish, a Help Desk Specialist at Wabash College, offered some ideas: “Send out blatantly obvious phishing emails with ridiculous email addresses and links to click.” According to Drew, after a year of testing, phishing click rates dropped nearly 100% on the harmful links.
By making these tests obvious, you exaggerate the indicators users should be looking for. On subsequent tests, you should be making these more difficult to identify for the user. Ultimately, your goal is to get this number down to 0%. Various stats out there exist, but varying reports show users acting on phishing emails at a rate between 10 – 30%!
5. Release the Results
After your penetration test, tell your company the results and compare that to previous tests. Inform them of the expected impact of their actions. For example, many people don’t understand the financial impact of a data breach. There are tons of reports that highlight this—finding that the average breach costs organizations .92 million!
No employee wants that big of a mistake hanging over their head. Hopefully, this will incentivize them to keep cybersecurity top of mind. When they can understand what is on the line when they aren’t making cybersecurity a priority (ex: large amounts of money, the business, their job, their co-worker’s job) they are more likely to take your training seriously.
If the results aren’t exactly where you’d like them to be, communicate your wants. Tell your employees the goal for next time, and if they obtain it, reward them with something like a pizza Friday or maybe even a monetary bonus for their dedication to keeping your business as safe as possible. After all, you wouldn’t be able to do it without their help!
Side Note: All this training and result-talk should also include upper management! It could happen to anyone, not just newer or inexperienced employees. If upper management falls for the phishing test, make sure they get the same education as the rest of the users. If you can get upper management to show support for your phishing tests, you’ll be surprised what a good example this will set.
6. Use a File Sharing Solution
When you can access your files via a file-sharing solution, you cut down on the likelihood of a convincing phishing email designed to look like a legitimate document making its way to your employees. Not only is your information encrypted, but with a file sharing solution, you don’t need to fear files being lost or corrupted. Your provider will be able to resolve your issues.
You also have permission control over who has access to what file and can even receive email notifications about file and user activity. And some file-sharing solutions, like SmartFile, offer visual tools and detailed logs to help you understand the usage. This way, you can easily identify outliers and protect your data.
With a solution like SmartFile, we can keep your files safe and your data secure. Employees might still fall victim to phishing scams or click on malicious links, but you can significantly reduce your risks and get some peace of mind when you share files with SmartFile. Contact us today to learn more about our solutions!